Authenticate
Analisi e rilevamento delle alterazioni in immagini e video
Il software completo che permette di rivelare la cronologia di elaborazione di immagini e video digitali.
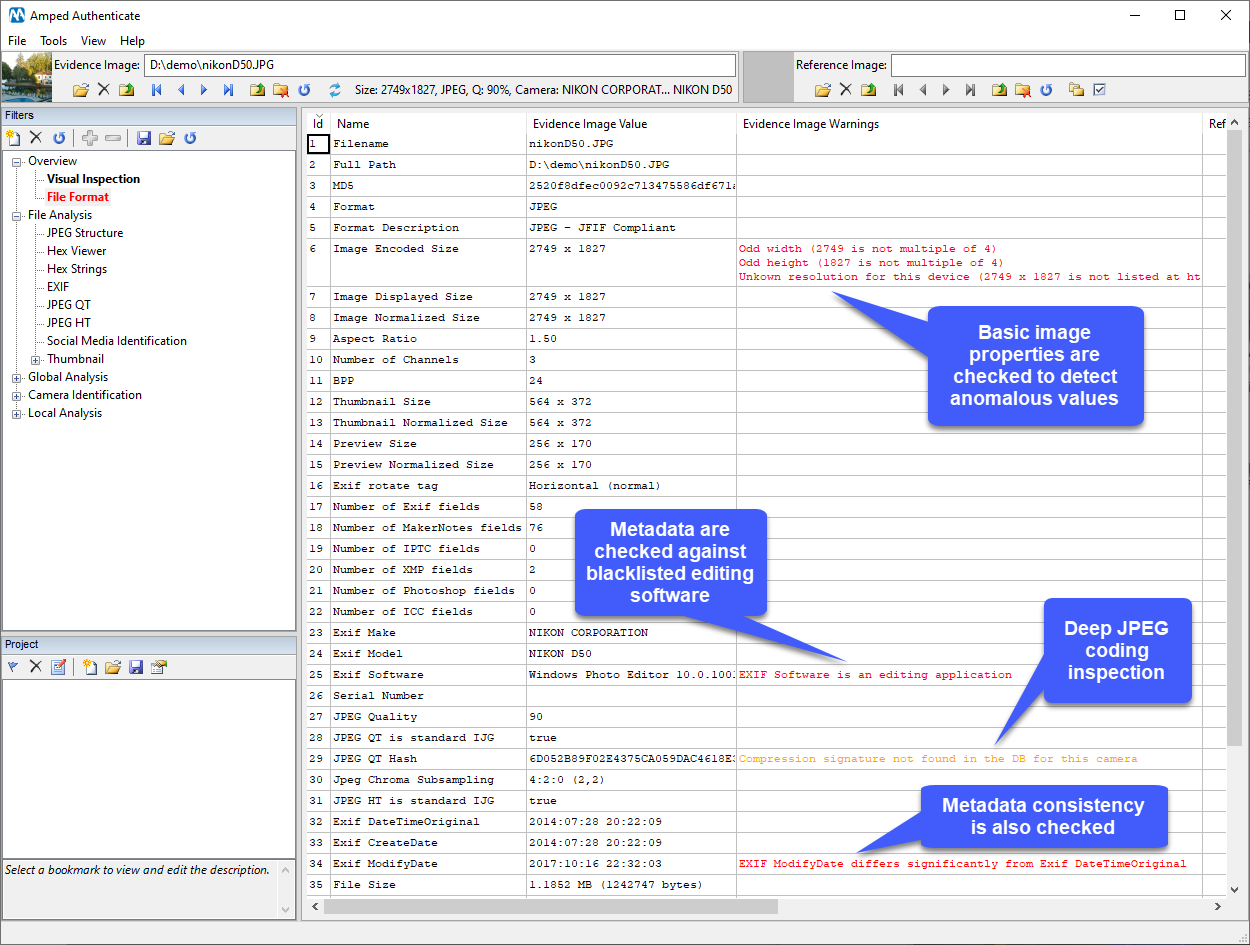
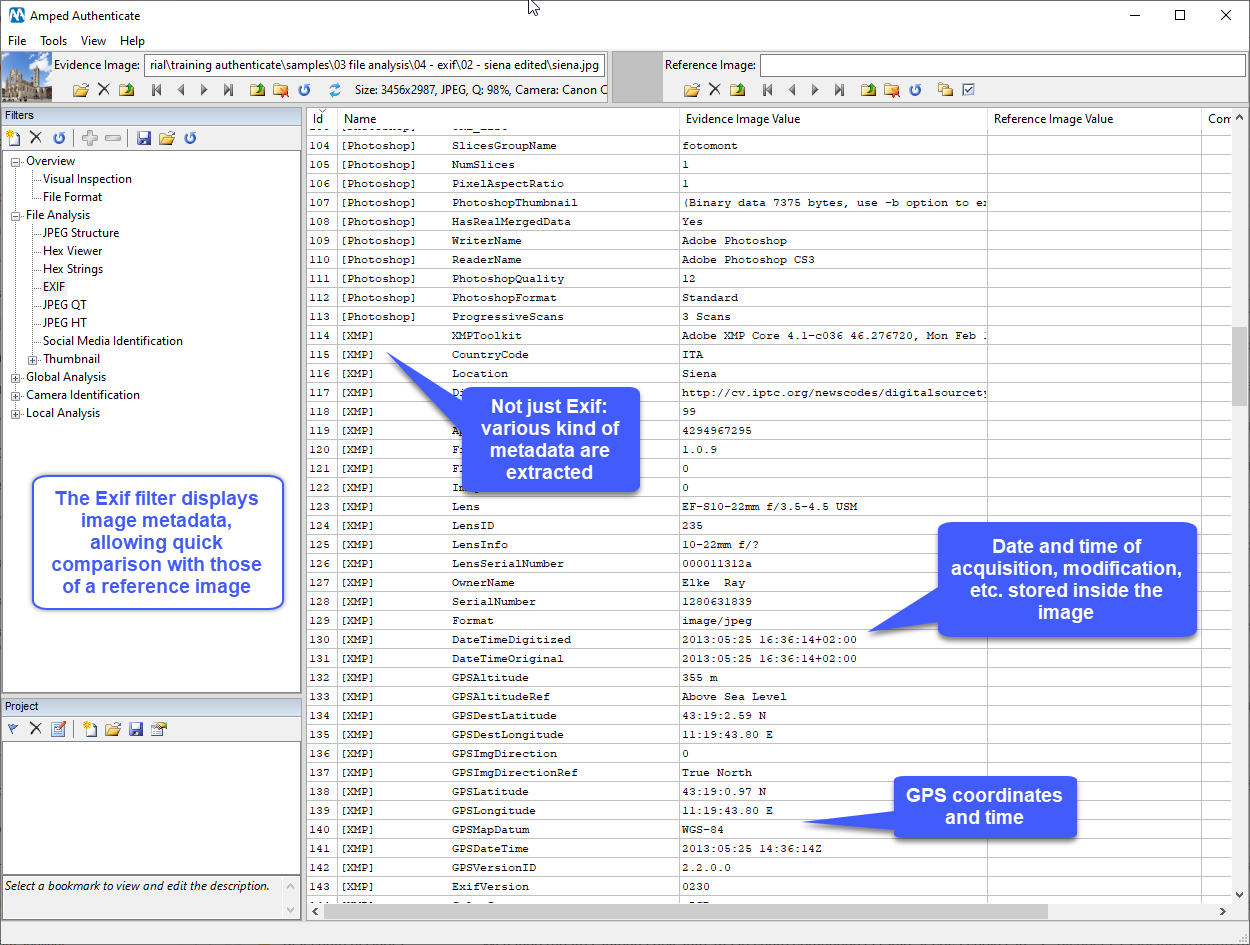
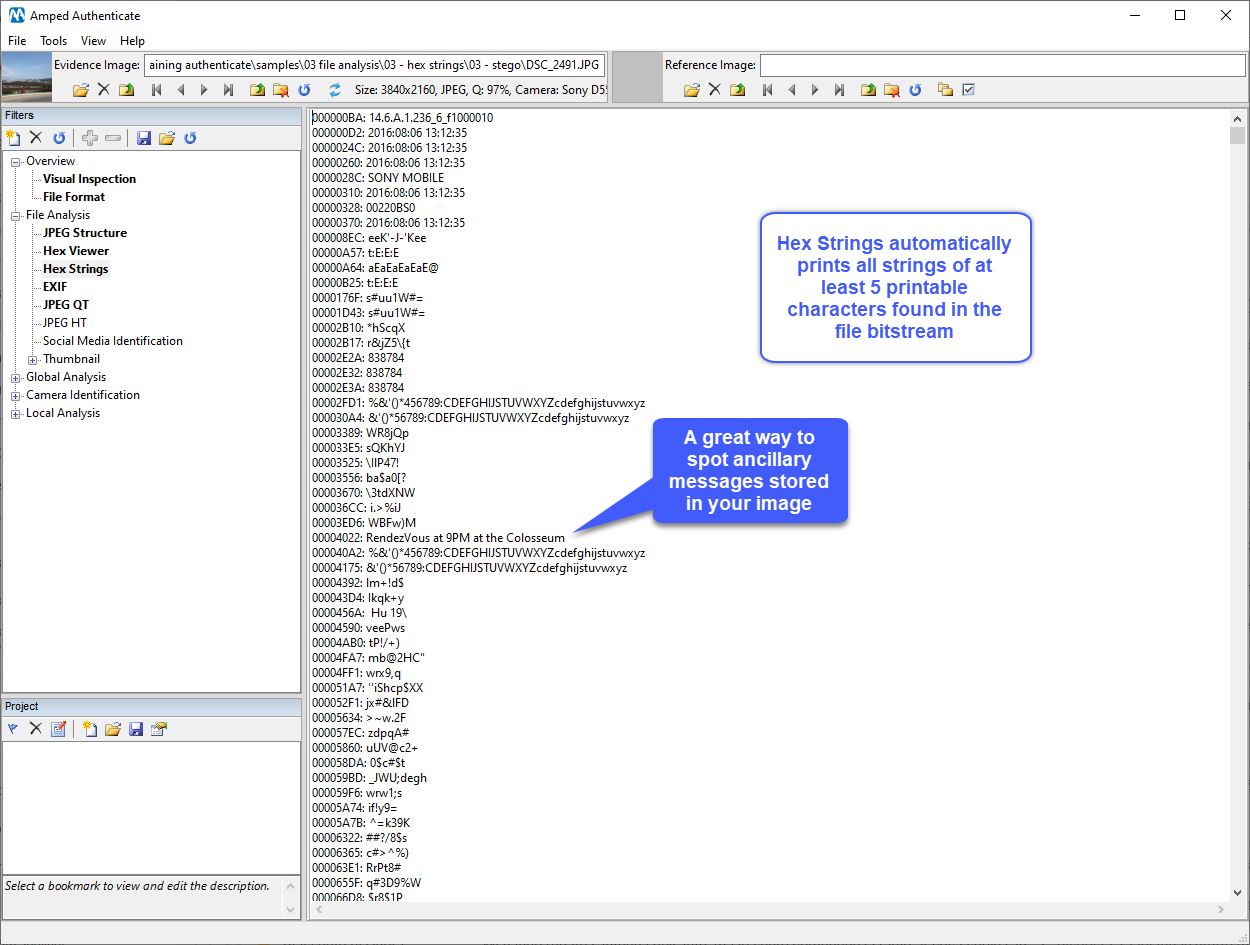
Consente di verificare l’integrità di immagini e video
Permette di identificare la cronologia dell’elaborazione subìta da immagini e video.
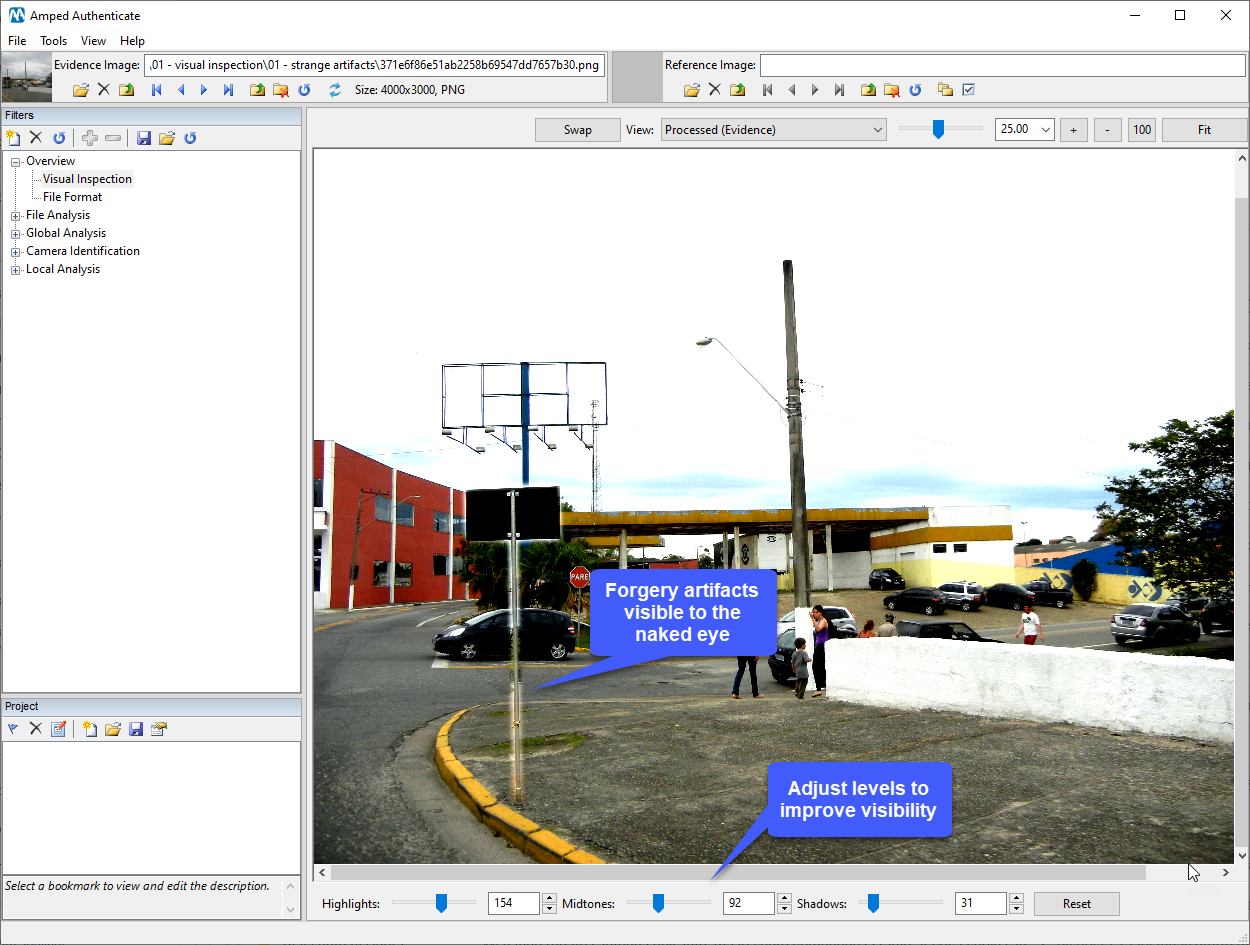
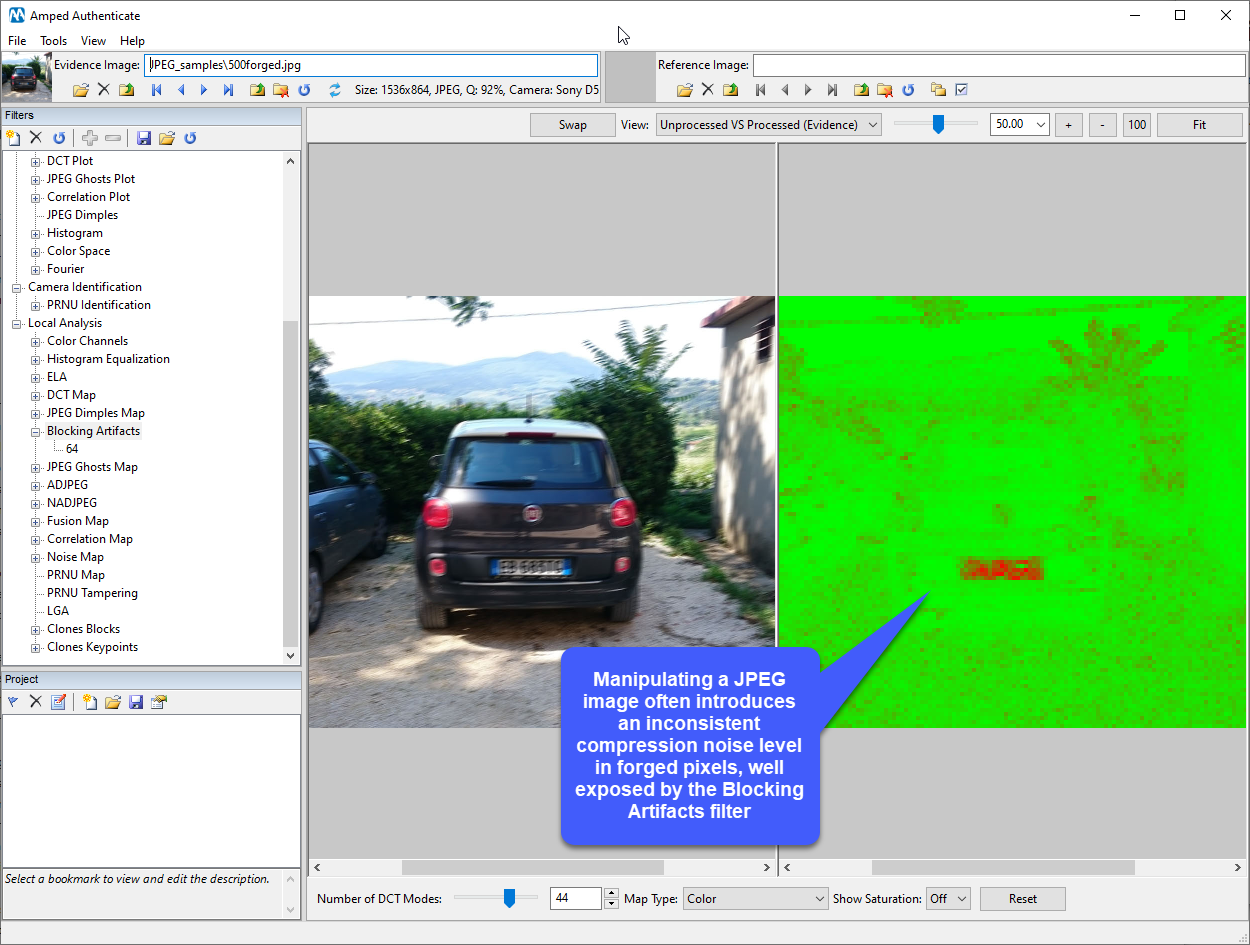
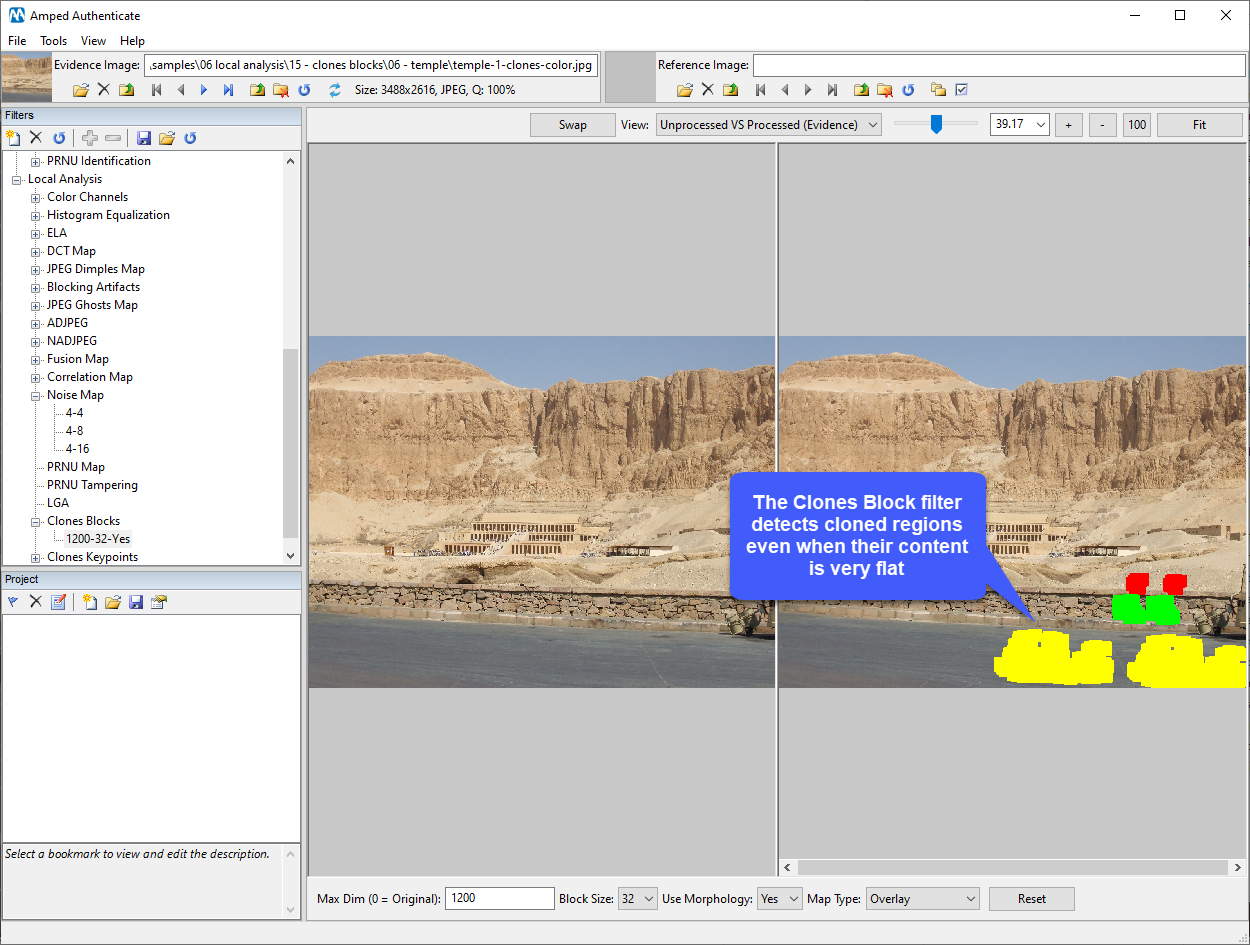
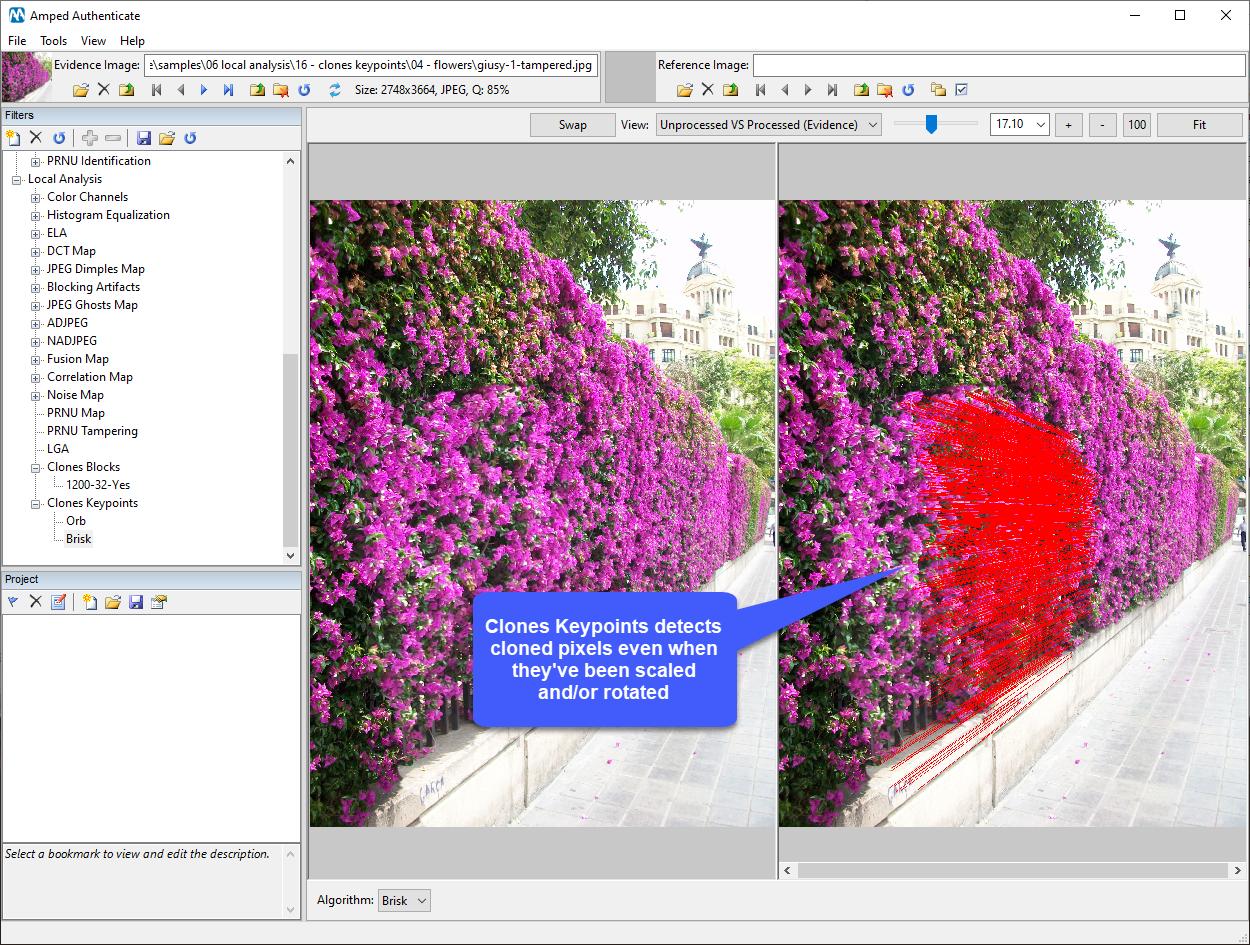
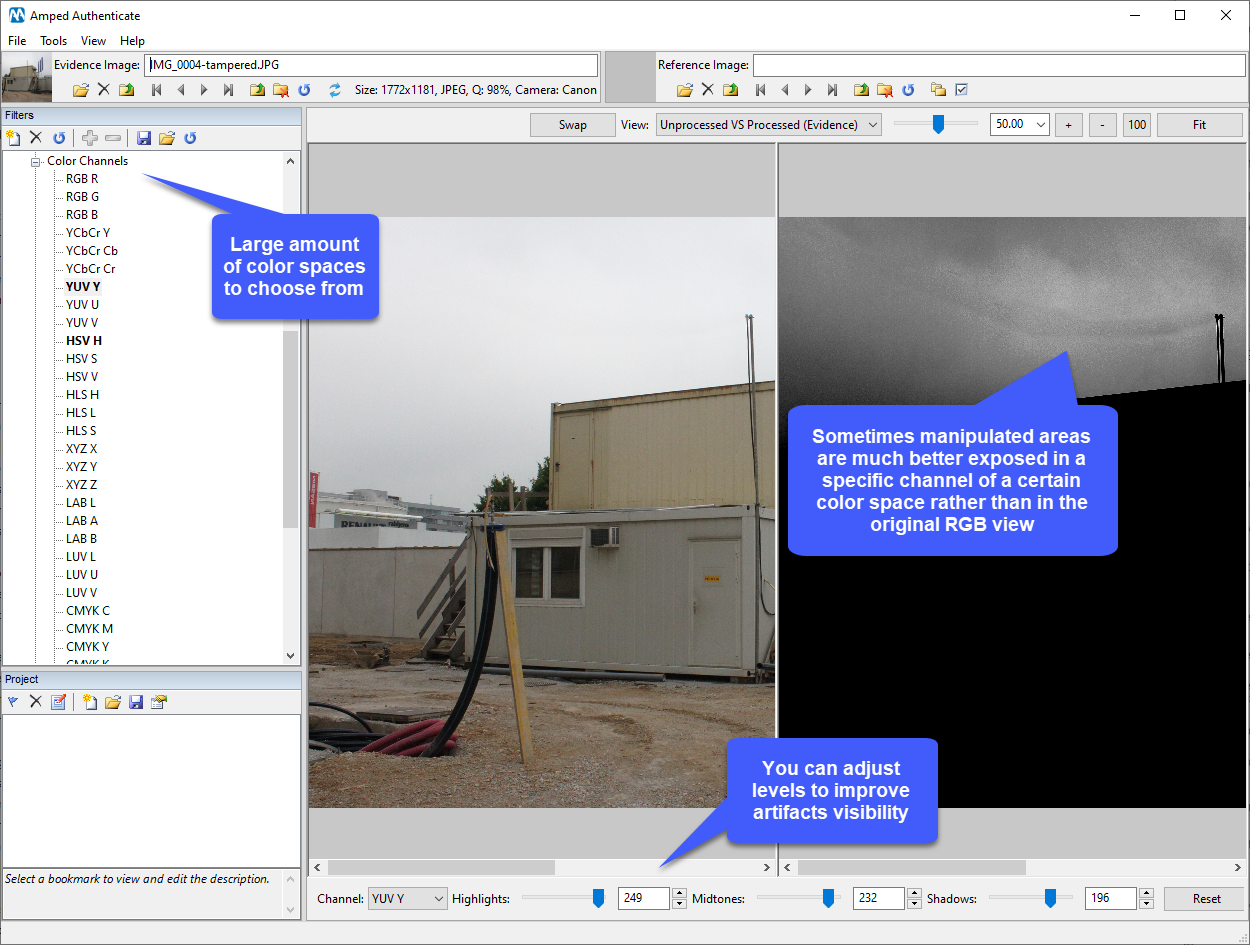
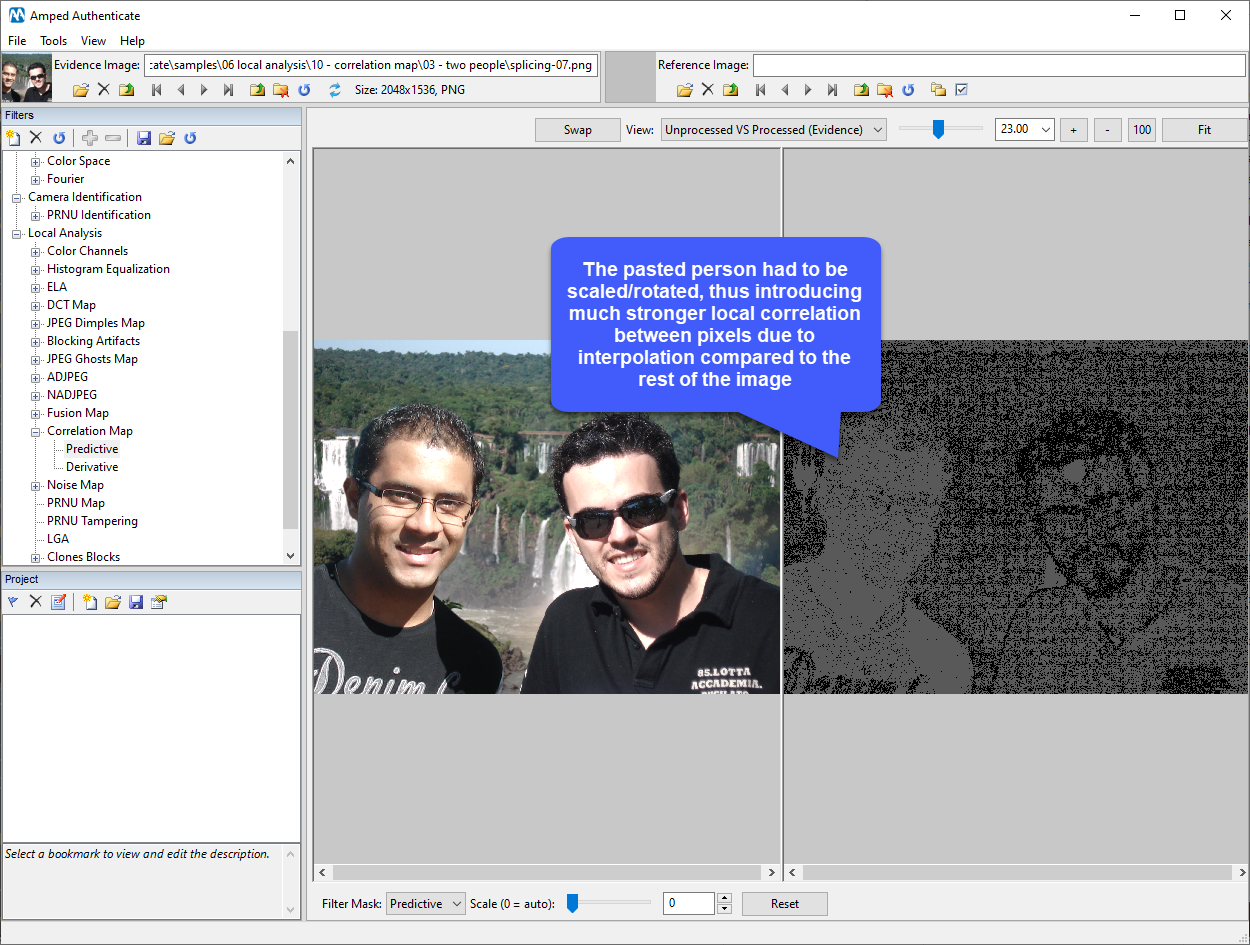
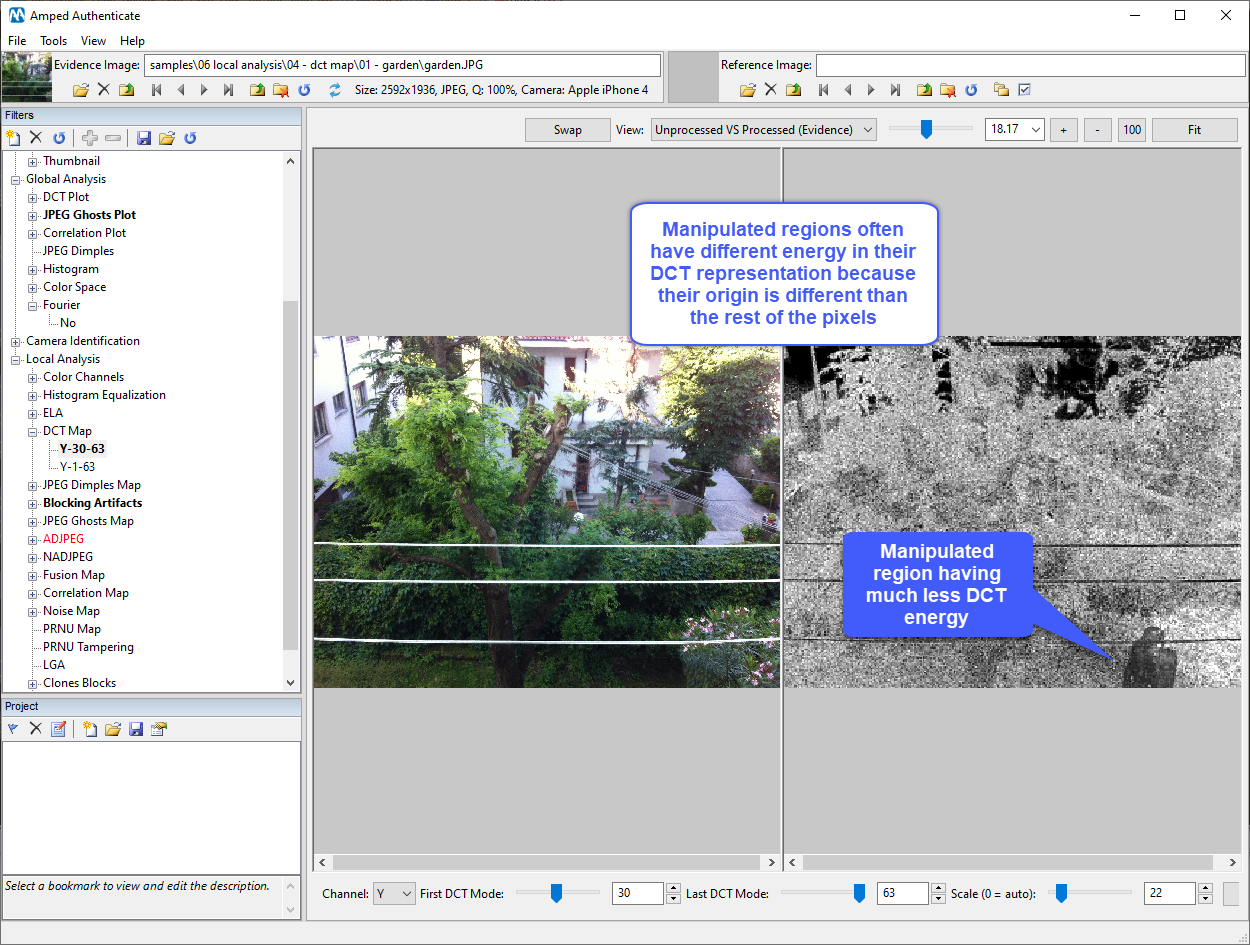
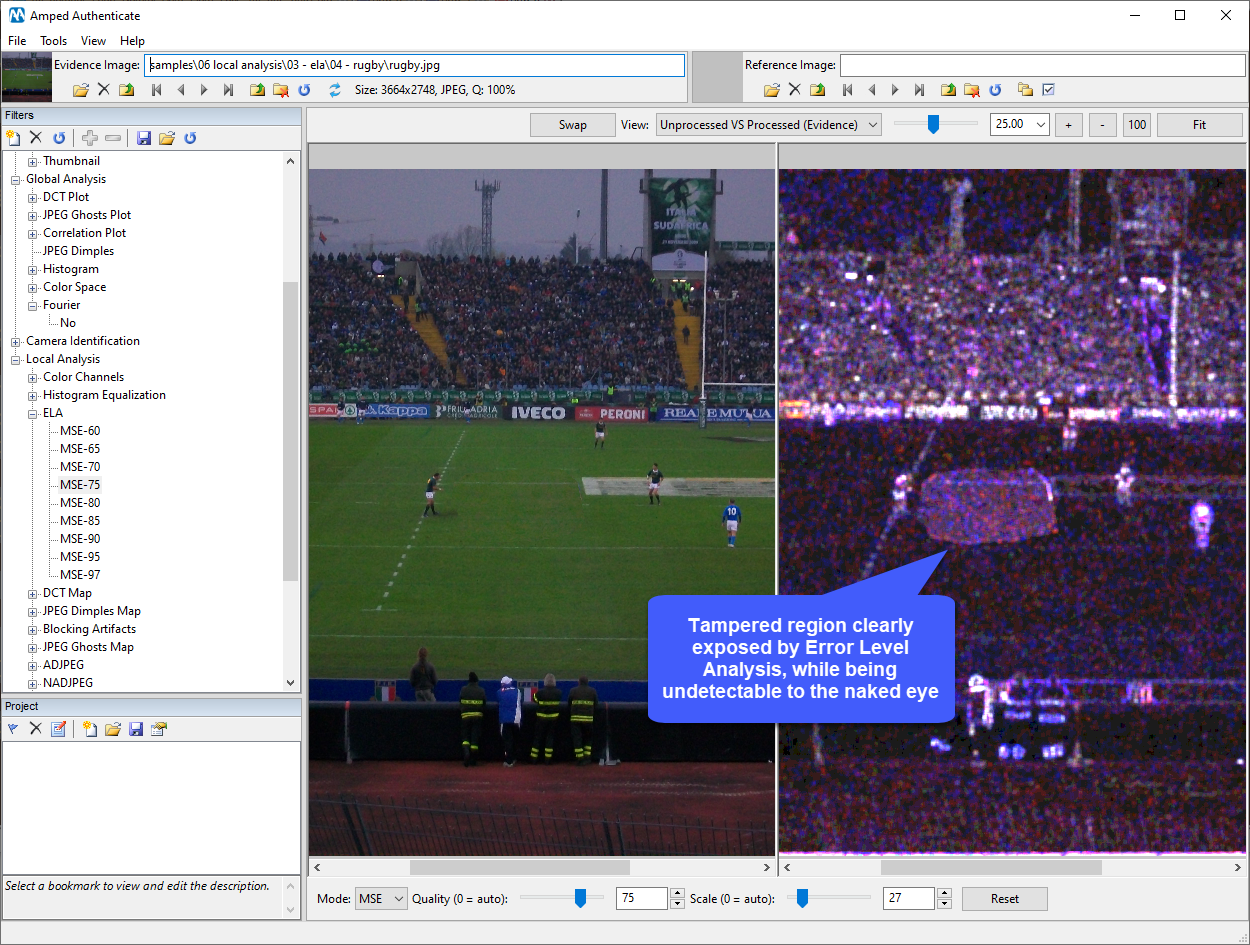
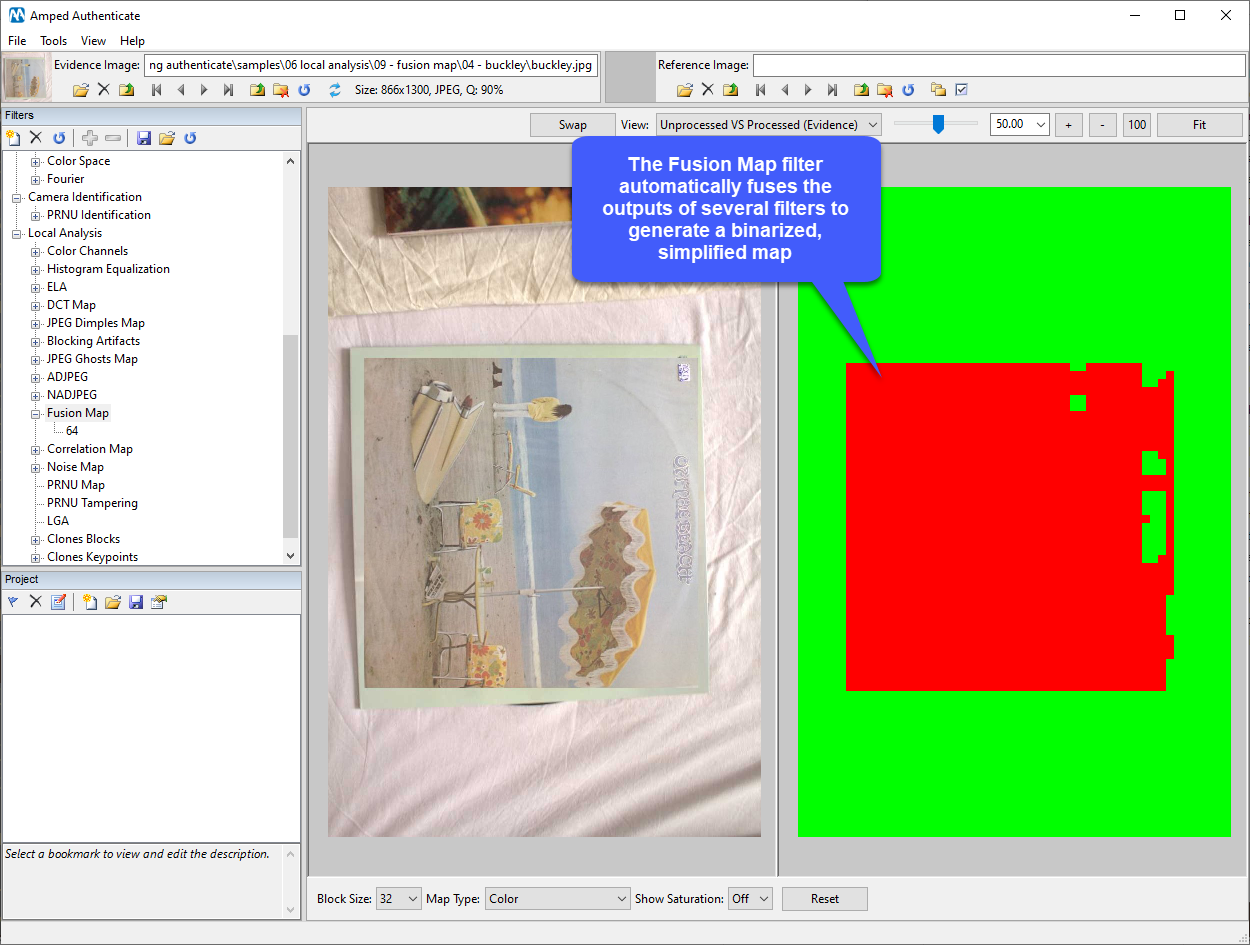
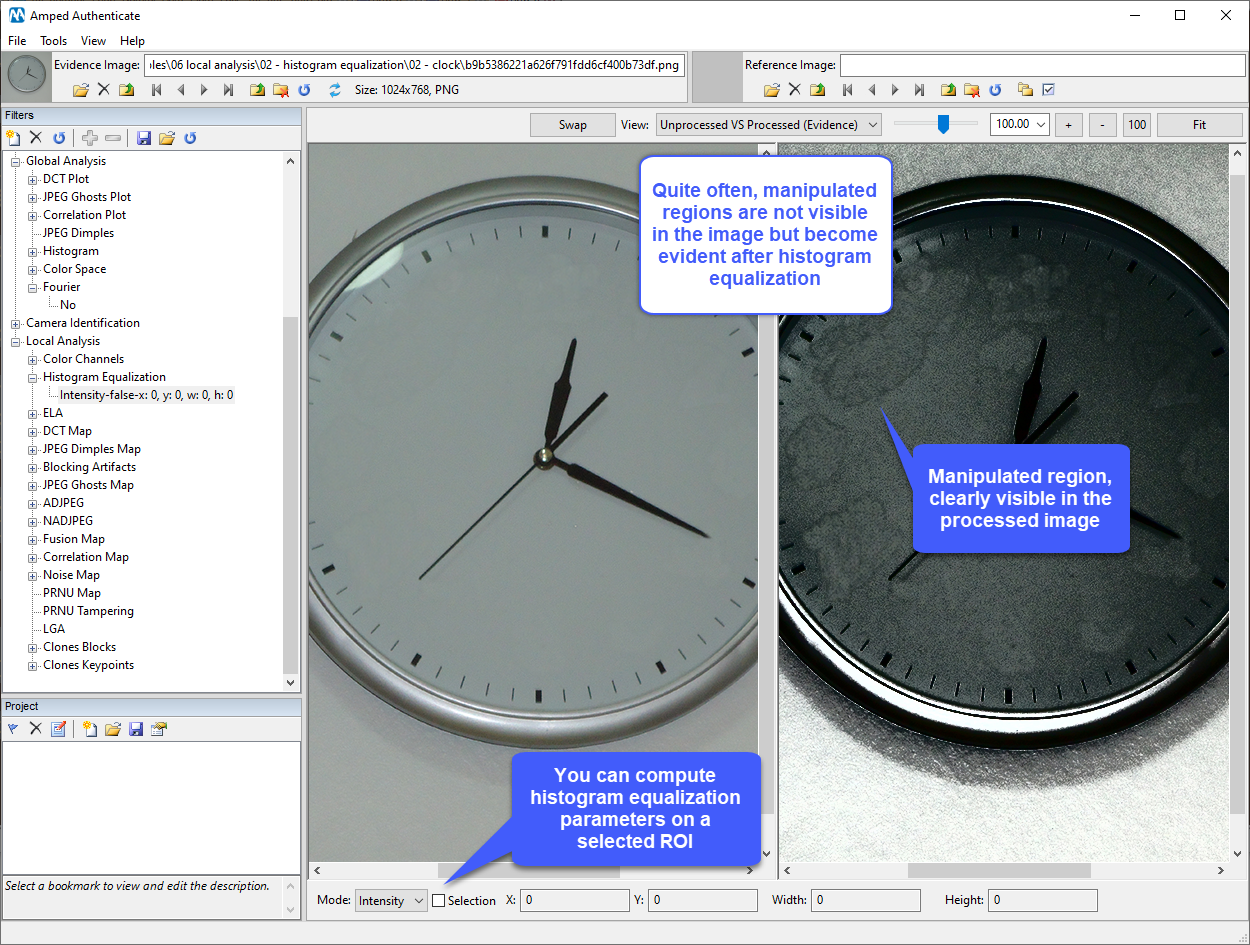
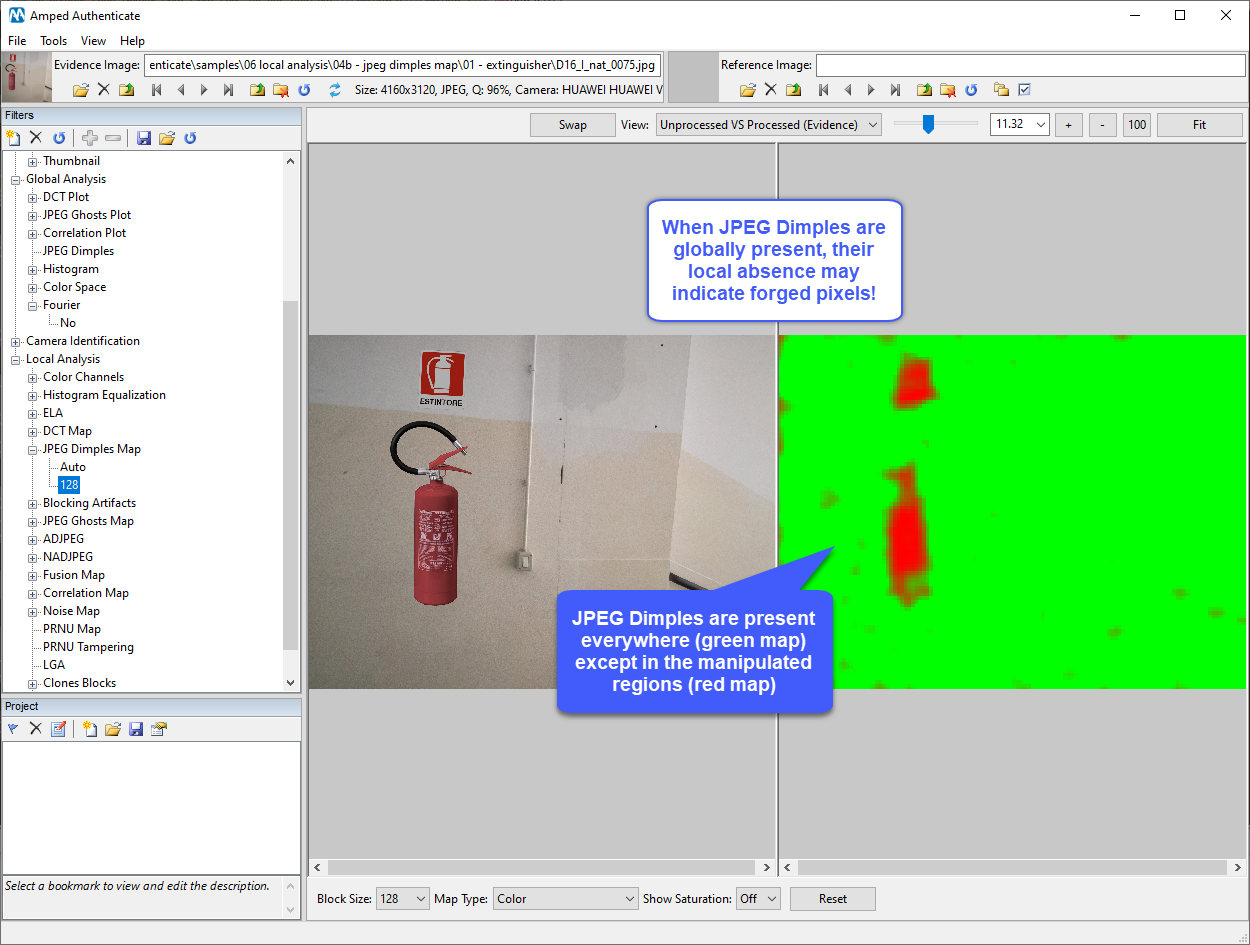
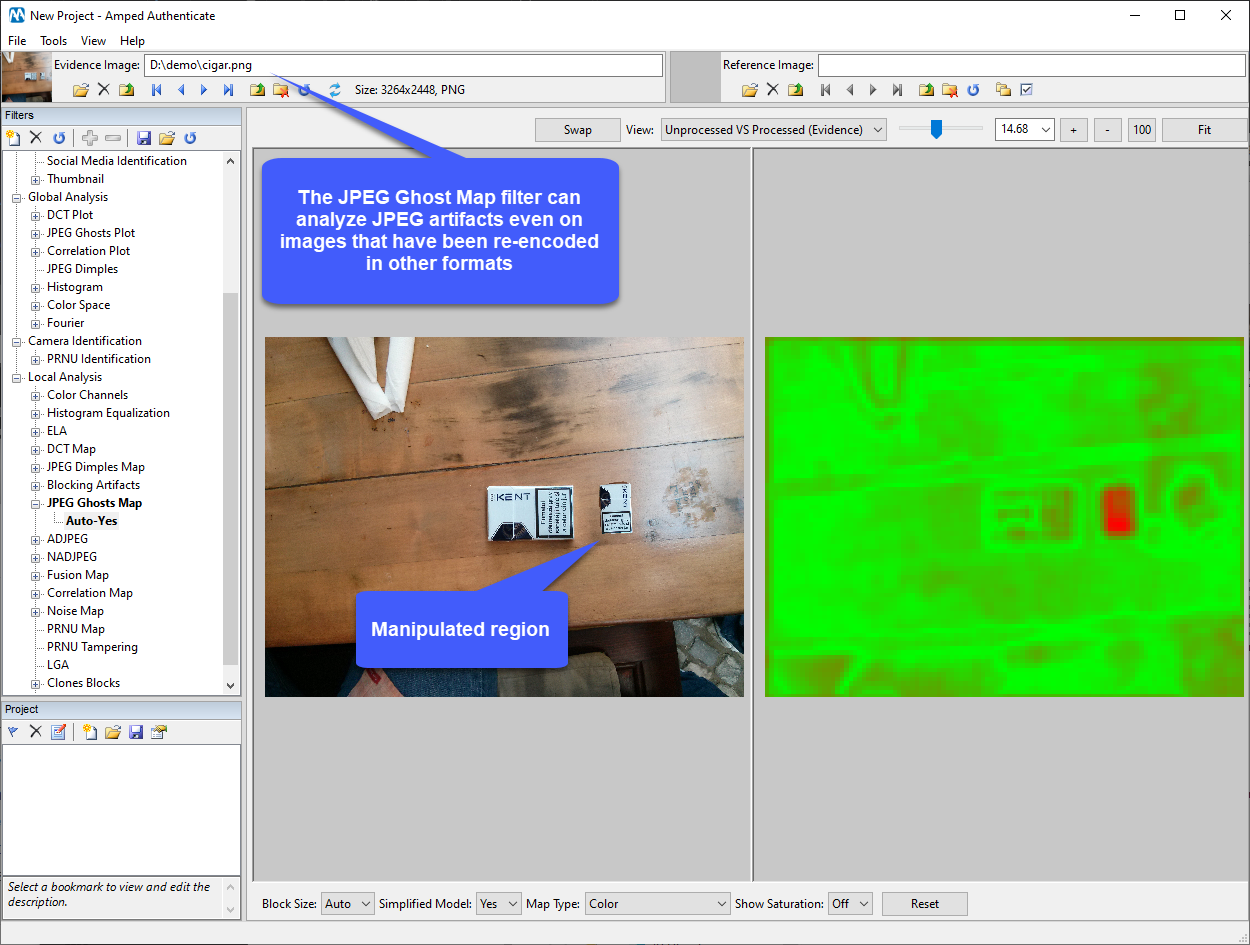
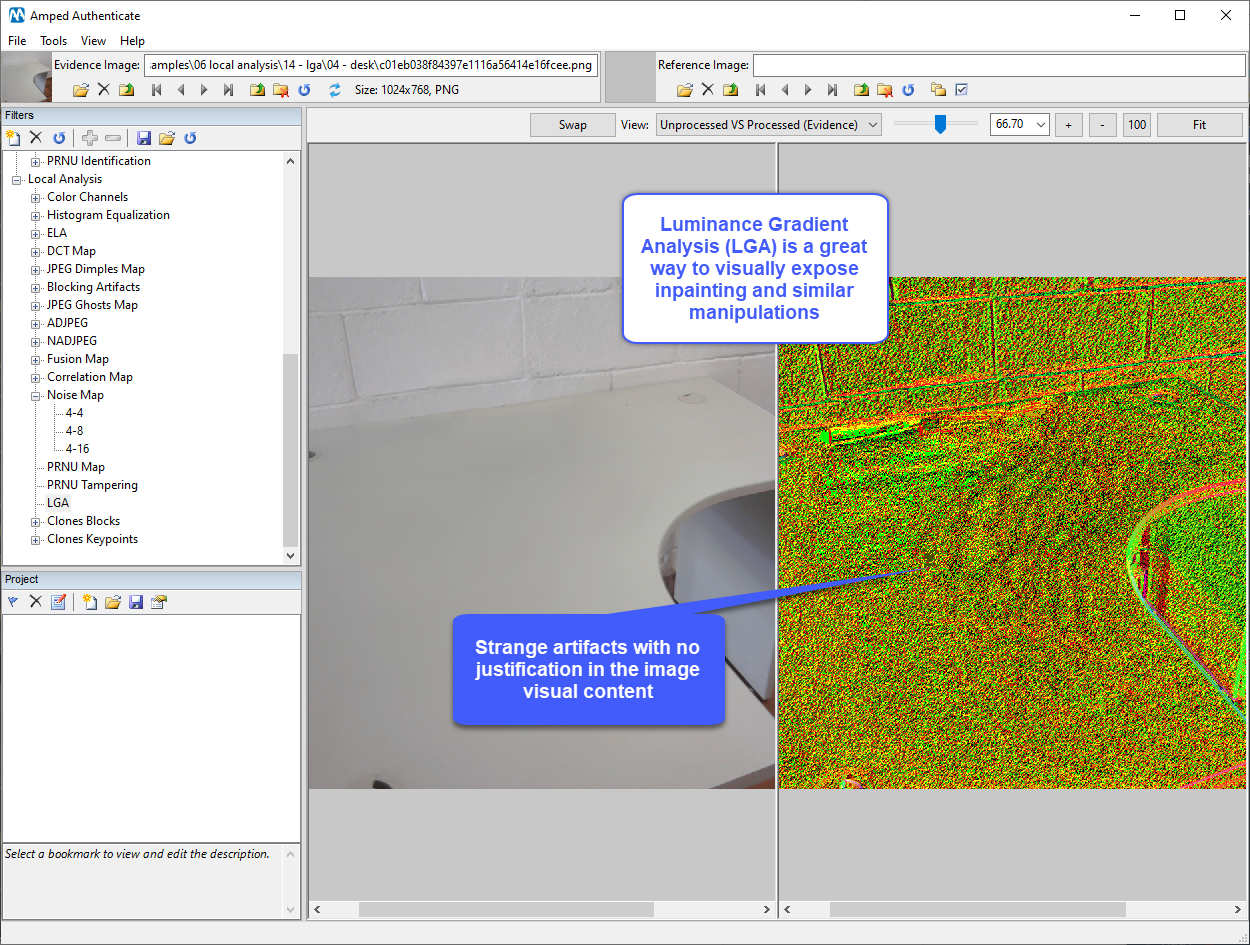
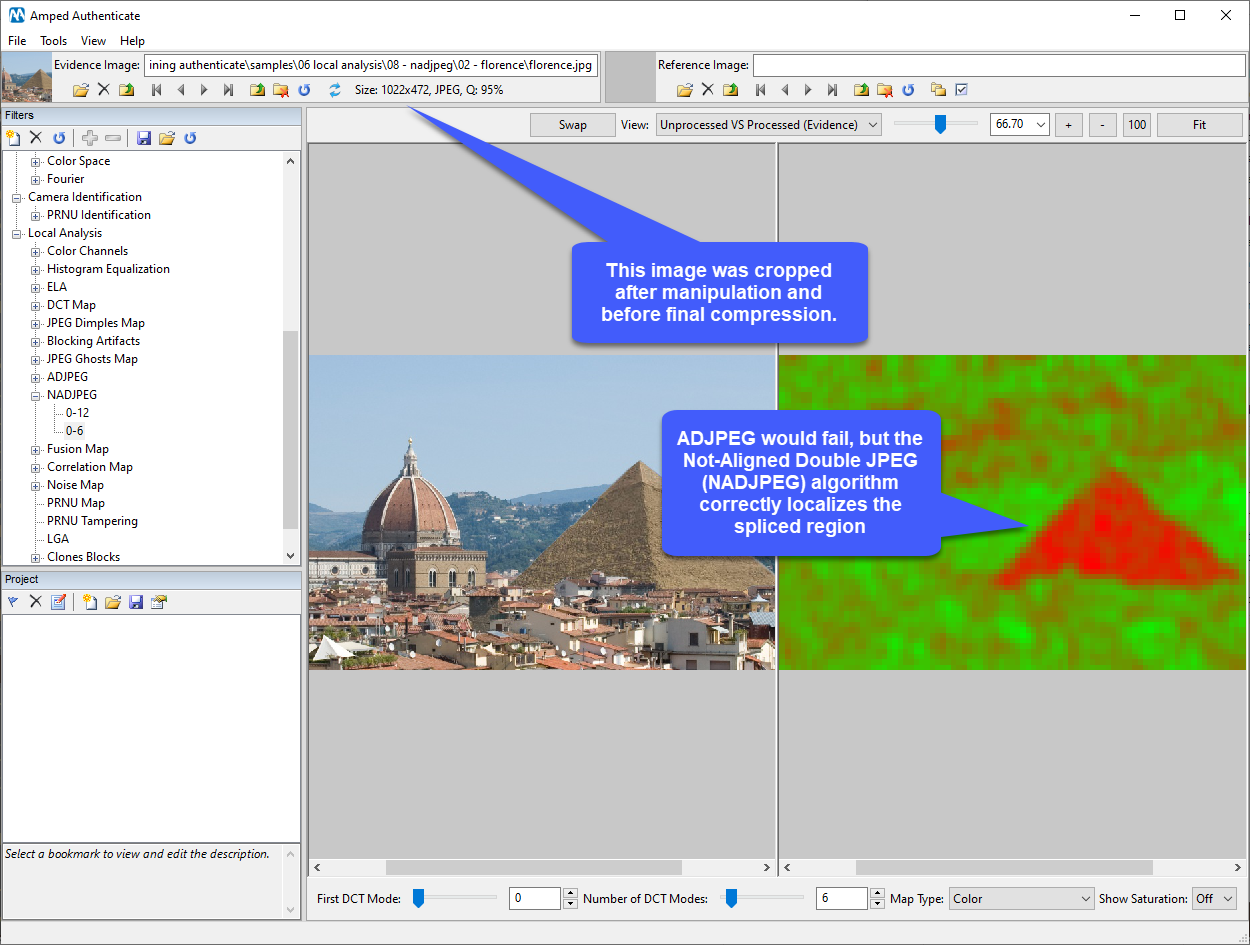
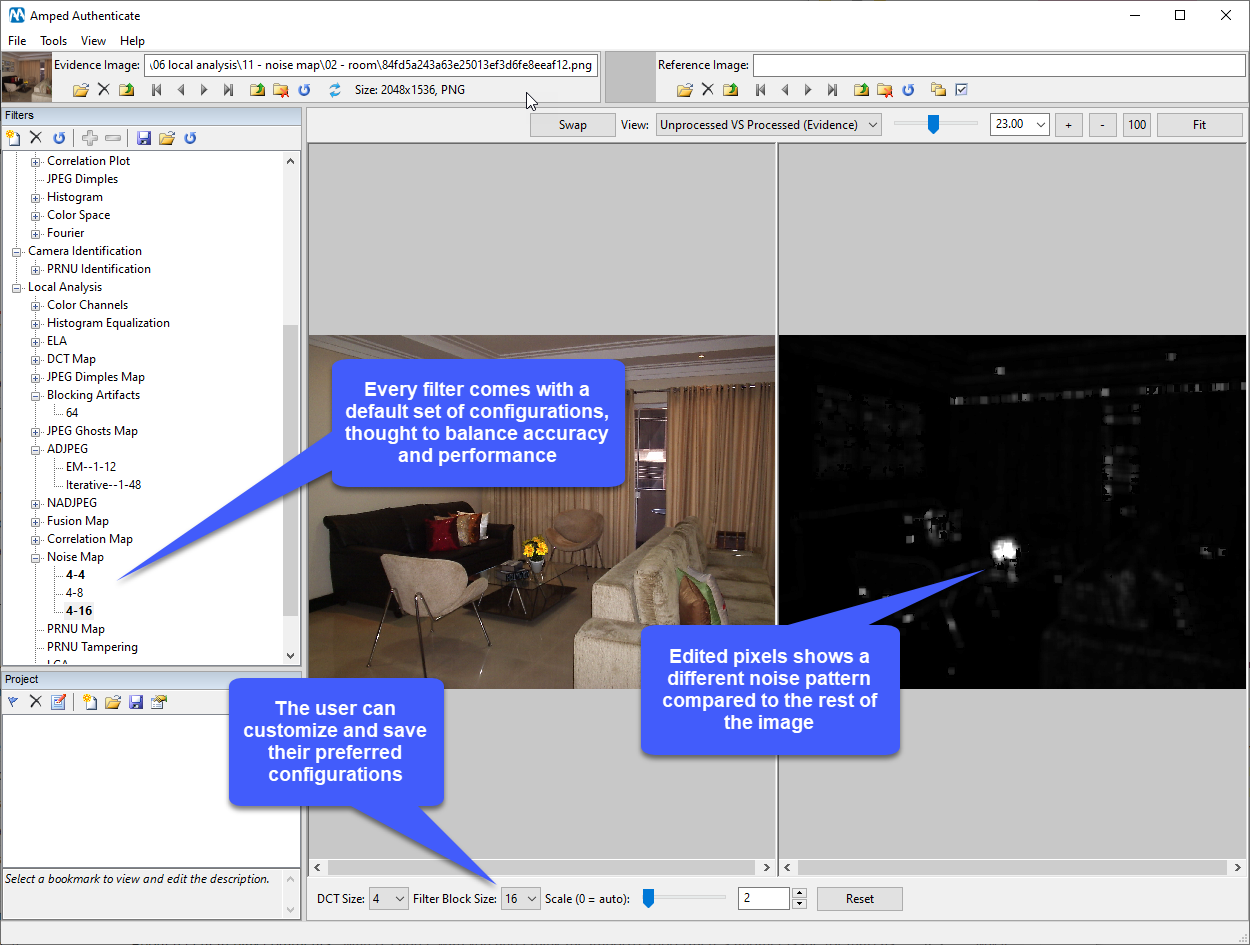
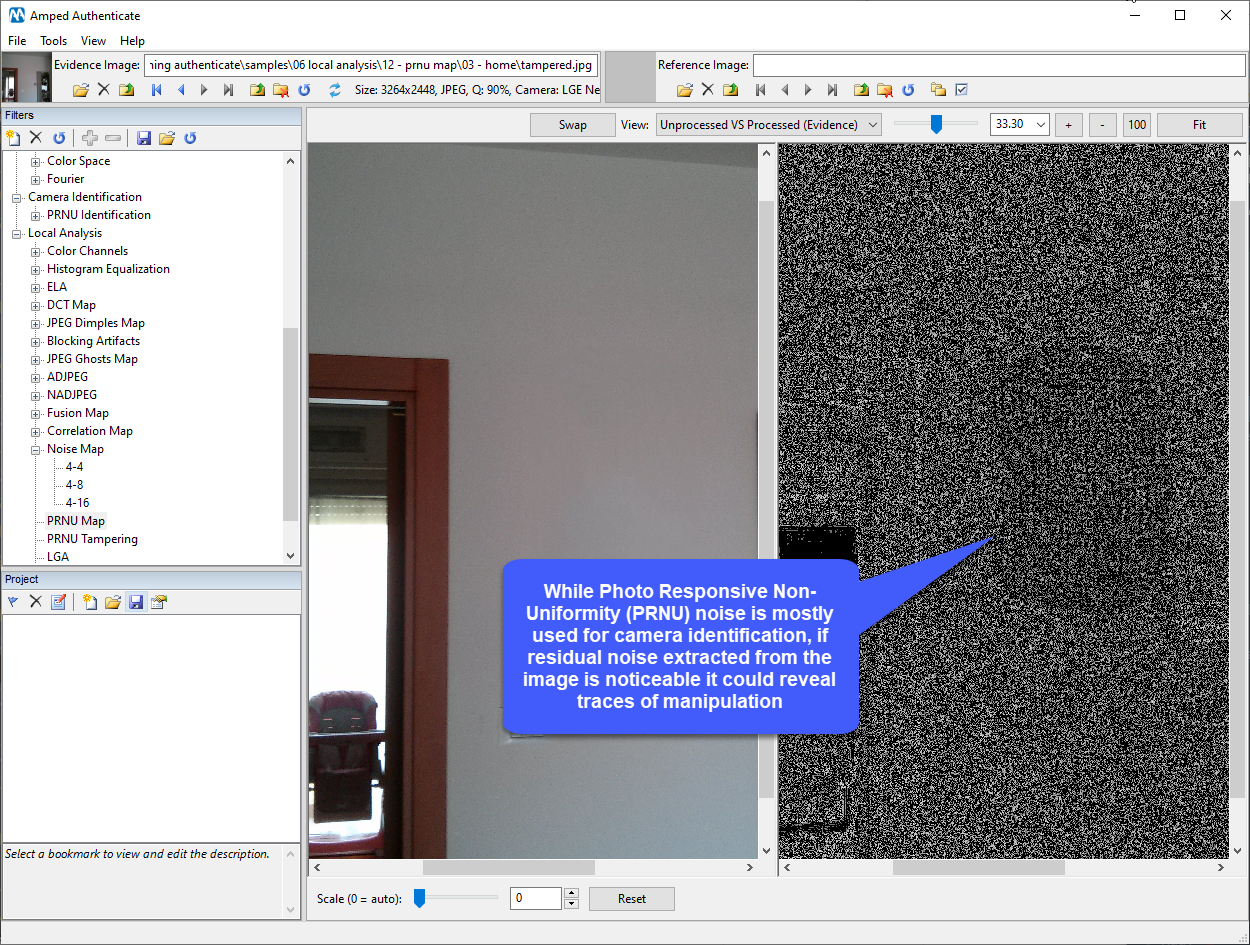
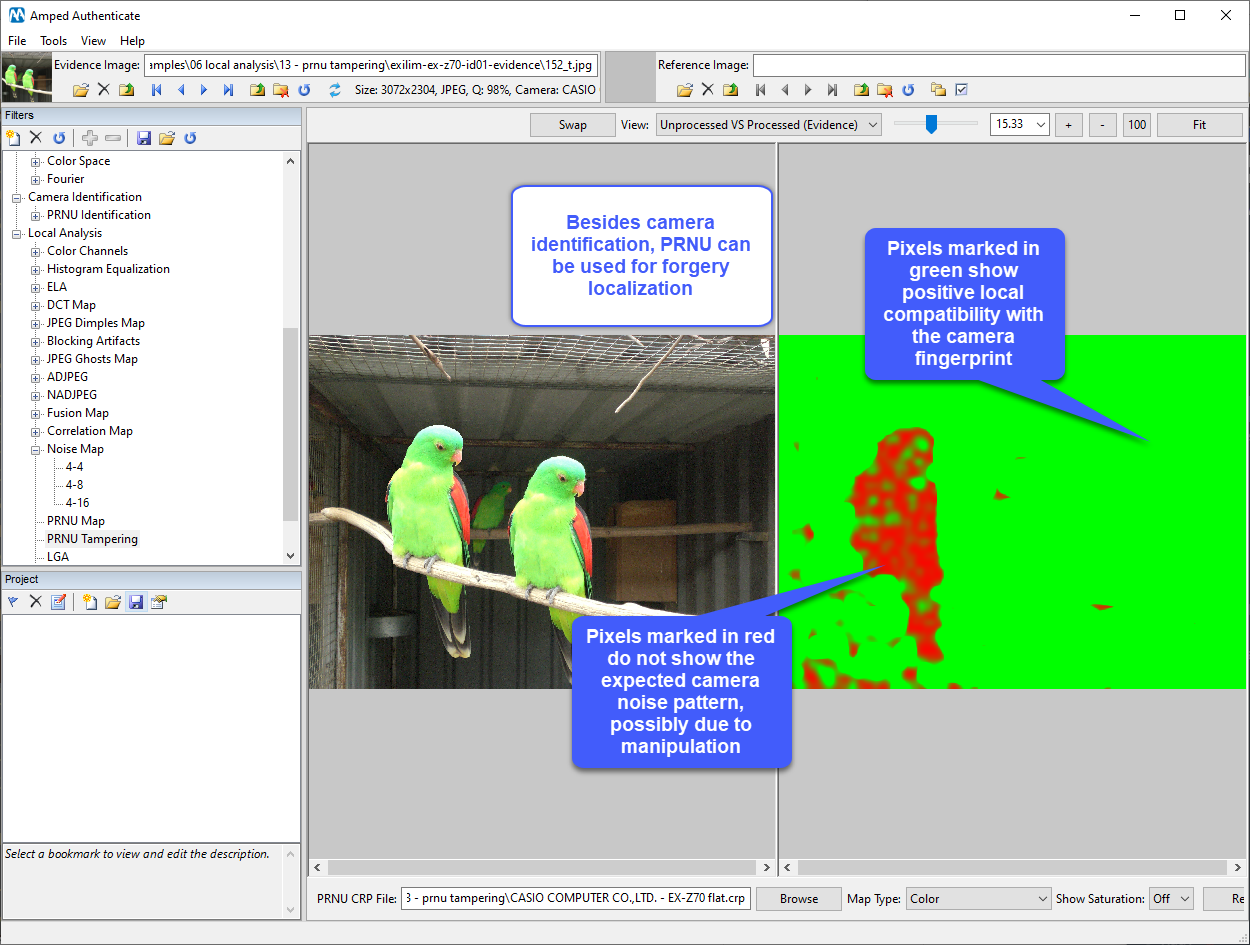
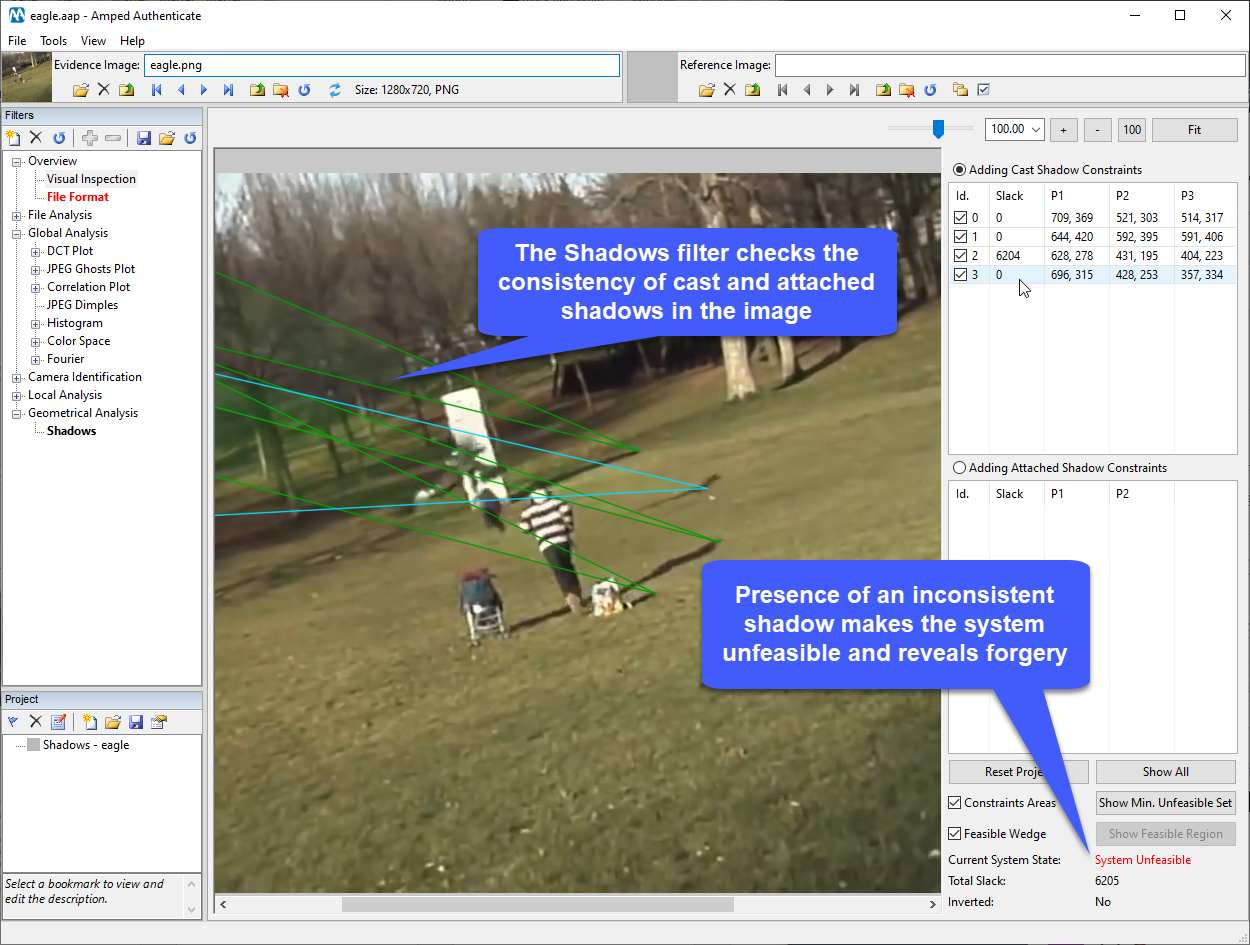
Rileva le aree manomesse per determinare l’autenticità dell’immagine o video.
Rende possibile identificare il dispositivo da cui ha origine un’immagine o un video.
Analisi e rilevamento delle alterazioni in immagini e video
Svela il processo di elaborazione di immagini e video digitali
Completo
Ammissibile in tribunale
Genera un report scientifico adattabile al progetto in essere, garantendo in questo modo la riproducibilità e la chiarezza dei risultati.
In assenza di solide basi a supporto dell’affidabilità delle informazioni, le immagini digitali potrebbero essere messe in discussione se presentate come prove durante un caso o in un’aula di tribunale. È perciò fondamentale nelle indagini di oggi poter esaminare a fondo un’immagine e dimostrarne l’attendibilità e l'origine.
Approvato
All’interno del manuale utente di Amped Authenticate sono forniti i riferimenti bibliografici per ogni filtro. Lo stesso avviene nel report finale, ogni qual volta un filtro viene utilizzato. Authenticate infatti contiene filtri di autenticazione di immagini e video basati su decine di articoli e studi scientifici. In Amped, quando implementiamo un filtro, realizziamo una validazione sperimentale per verificare la corrispondenza con le prestazioni riportate in letteratura.
Autenticazione di immagini e video
Amped Authenticate aiuta analisti ed investigatori a chiarire i numerosi dubbi che oggi sorgono riguardo l’autenticità e l’integrità delle immagini digitali.
Caratteristiche
Chi utilizza Amped Authenticate
Il software viene utilizzato, tra gli altri, da esperti forensi in ambito digitale e da agenzie di intelligence in tutto il mondo.

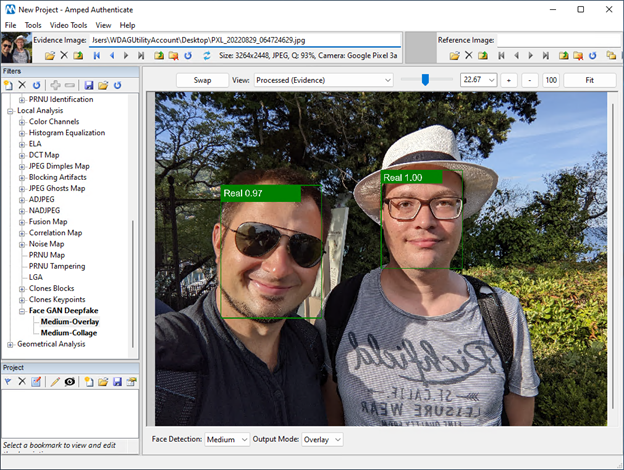
Il filtro Face GAN (Generative Adversarial Network) Deepfake
Analizza immagini e video
Per prima cosa, il filtro Face GAN Deepfake individua i volti all’interno dell’immagine e utilizza poi l’IA per classificare ogni volto ed assegnarvi un punteggio da 0 a 1 secondo il grado di sicurezza. Se tale punteggio è superiore a 0.8, l’etichetta può riportare la scritta Autentico (colore verde) oppure Falso (colore rosso).
Se invece il punteggio è inferiore, Authenticate avrà un approccio più cauto e scriverà Possibile Autentico o Possibile Falso.
100+ Articoli “How-to”
Scopri di piùAccresci le tue competenze nell’ambito dell’autenticazione di immagini
Amped Ultimate
Team subscription
Per gruppi di quattro o più persone incaricate dell’analisi video forense
L'abbonamento annuale comprende:
- 1 postazione Amped FIVE
- 1 postazione Amped Authenticate
- 1 postazione Amped DVRConv
- 5 postazioni Amped Replay
Dal nostro